Solutions
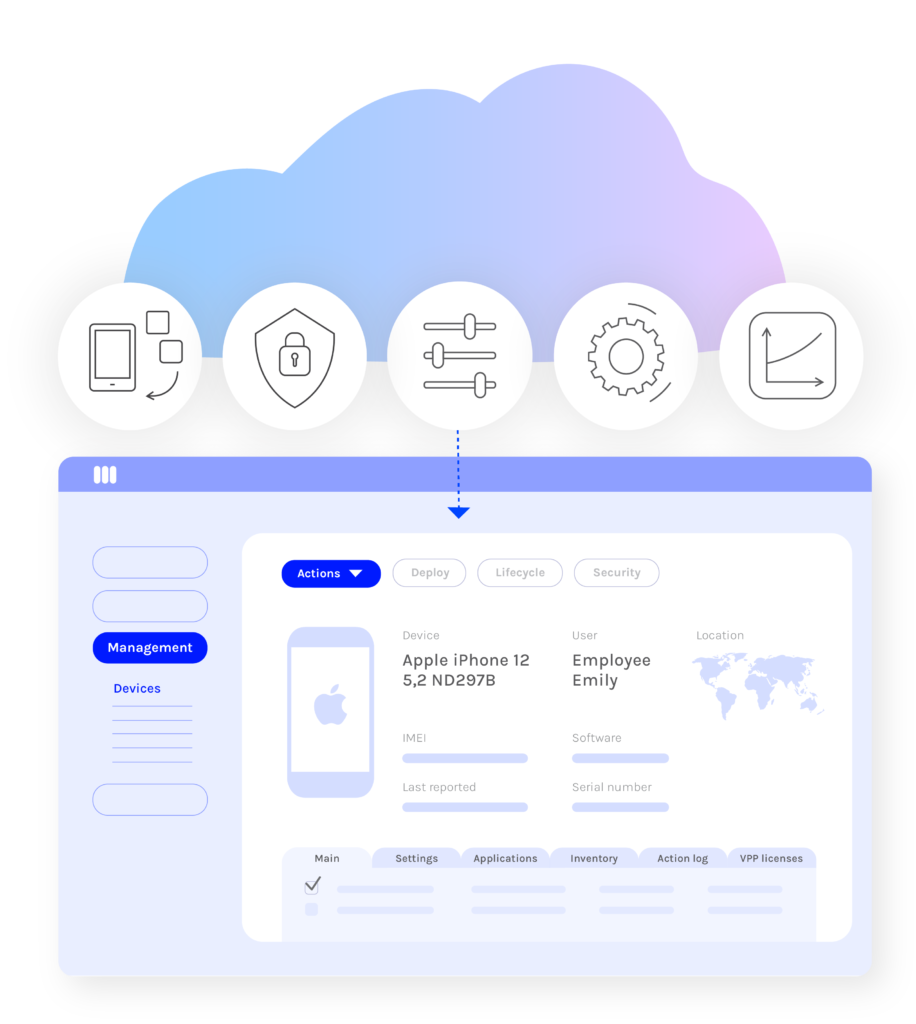
Mobile Device Management (MDM)
Miradore is an easy-to-use, cloud-based MDM software for Android, iOS, Windows, and macOS that helps organizations effectively manage the use and security of their mobile endpoints. It’s very easy to implement and takes just a couple of minutes to get started on.
Miradore in 2 minutes
Mobile Device Management from the cloud
Most organizations work hard and invest heavily in protection for their workstations and PCs – rightfully so. But securing mobile devices is equally important as they are often used for storing and processing sensitive data.
Miradore Mobile Device Management (MDM) solution has various features that help you to ensure security and compliance on all your mobile devices easily and cost-efficiently. Furthermore, efficient mobile device management enables your employees to work without interruptions.
Benefits of MDM
Secure data and devices
A lost device doesn’t have to mean lost data. Miradore helps you manage IT risks by offering an effective way to safeguard your devices and the data they carry. You can enforce safe passcodes, screen locks, work profiles, and containers, and encrypt all confidential content. Mobile Device Management software also helps your organization become and stay compliant with increasing data protection regulations, such as GDPR and HIPAA.
Save time with IT automation
Mobile device management with Miradore translates into online efficiency and security. New device roll-outs and are fast and efficient by automation. You can save time and money by deploying business policies, automating installations and patch management, and enforcing configurations, applications and more. Disposing manual tasks will reduce human errors and help ensure compliance and secure use of mobile devices.
Manage devices cost-efficiently
With Miradore, you can manage company-wide device enrollment cost-efficiently, saving up to 30 minutes per device. New sites can be created in seconds and configured in minutes, and we offer a powerful API to adjust Miradore to your business needs. Our clients report significant cost savings thanks to the flexible need-based, pay-as-you-go licensing model.
Increase visibility
Miradore pulls hundreds of data points from managed devices and translates the data into easy-to-understand yet insightful reports and visual dashboards. Comprehensive and real-time analytics lets you make informed decisions, know your devices inside out, and manage security risks.

“Since we started using Miradore the management of our devices has greatly simplified and improved. The ease of use, reliability, and speed of the software gives us the opportunity to focus on other important things.”
Kevin Rijnders, Pepperminds
“Miradore has dramatically increased the ease with which we manage our devices – the interface is intuitive and extremely simple to navigate.”
Billington Food Service
