What is patch management?
Patch management is a process in which code changes, “patches”, are deployed to devices to fix or update the device’s operating system or software products. Patches are small installation packages or files that are installed on computers.
First and foremost, patch management helps prevent data breaches by fixing security vulnerabilities. It also makes it easier to ensure that devices are running the latest software versions. Patch management is an essential part of Windows and Mac management.
Why is patch management important?
The main purpose of patch management is to ensure the security and performance of devices.
According to a study by Tripwire, almost one-third of organizations have suffered a data breach due to an unpatched vulnerability. A study by Ponemon Institute and ServiceNow shows similar results. Almost 50% of the respondents report having had one or more data breaches in the past two years, and 60% of breached companies say that those breaches may have occurred due to an unpatched known vulnerability.
Unpatched software is a real cybersecurity risk for organizations, which can result in data breaches that have multifaceted consequences. Luckily, security risks can be mitigated with efficient patch management practices.
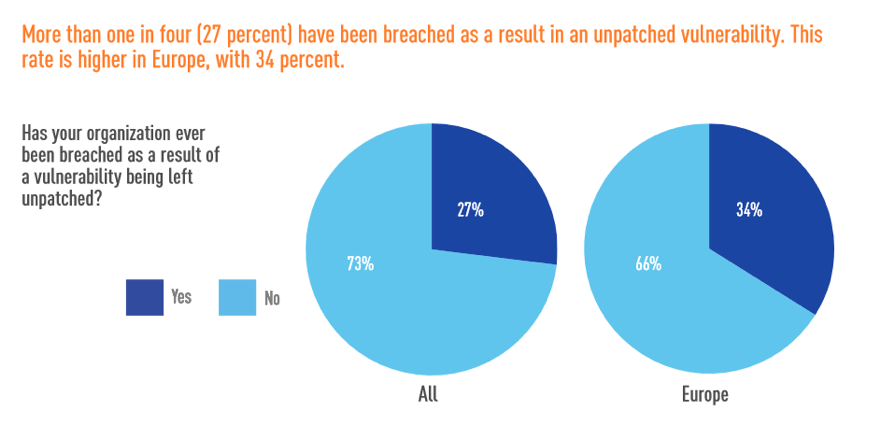
Source: Tripwire
Furthermore, patching helps ensure the performance and stability of operating systems and applications. Patches typically include important software updates which tackle performance issues and remove outdated features.
Benefits of patch management
So why should your organization utilize patch management? Here are three major reasons:
- Device and data security: Fixing security weaknesses with the latest software patches helps you prevent data breaches in which sensitive customer or company data can leak outside your company.
- Compliance: Patching helps you make sure that unauthorized people can not access your data and exploit it. Proper data storing and handling is also a prerequisite for complying with regulations, such as HIPAA and GDPR.
- User experience: With patch management, you can ensure that devices are running smoothly without interruptions. Productivity increases as device users don’t have to struggle with performance issues or bugs.
Manual or centralized patch management?
Operating systems and applications can be updated either manually or centrally with patch management software. If you're managing only a few computers and can easily keep track of your devices, manual patch management might work for you.
However, hundreds of software patches are being released continuously for different applications and operating systems. Without an automated process, staying on top of those can be a complex, if not impossible, task.
If you're managing multiple devices and need to keep track of their patching status, you might want to consider centralized patching.
Using patch management software makes it easy to centrally monitor the patching status of your IT environment. It also allows you to upload and install all necessary patches to your devices automatically. This means that your IT Manager or device user doesn't have to manually search for new patches and install them separately.
There are several patch management solutions in the market, but having patch management as part of your Unified Endpoint Management solution makes device management significantly easier. With a UEM solution, you can view detailed information on your devices and manage other security configurations for your Windows and Mac computers.
Patch management process and best practices
Before you get started, it's good to take a more strategic approach to your patching process rather than just start installing new patches immediately. We recommend using patch management software and creating a patch management plan that takes the following things into account:
1. Up-to-date asset inventory
The number one rule is to always have an up-to-date device inventory to identify potential security threats. It's essential to know which devices you have in your IT environment and have access to detailed hardware and software information (e.g., operating systems, versions, locations, and device users).
2. Patch detection
Make sure to stay updated on the latest patches for your devices' operating systems and applications. Patches can be searched manually but patch management software enables you to automate the detection — ensuring that you don't miss any critical updates.
3. Patching status
Before approving or deploying any patches, try to get a comprehensive understanding of the patching status of your software and computers. You can do this easily by running a patch scan on your devices with patch management software. Identify what are the most common and crucial patches that are missing from your computers.
Also, check which patches have been superseded by newer ones. You might not want to deploy those that have already been replaced by newer patches.
4. Patching plan
Before you start approving the patch deployments, it's recommended to spend a while planning your patch management policies. Here are some questions and tips to help you with this:
- Which patches are you interested in? Make a list of software applications that you want to patch.
- Review and verify your list against the results of the patch scan. Make sure your list is not unintentionally missing any software that has been detected in the environment.
- For how long should the patch deployments be tested? When do you estimate to get results from the pilot group?
- How soon should new patches be applied to managed computers?
- Who is responsible for overlooking the patch management process?
- Should users be informed about patching activities? We recommend informing at least the pilot users about new patch deployments so that they can report back the possible problems.
5. Patch approval
Depending on the patch management software or method you're using, you can approve patches either manually or let automation handle that for you. Manual patch approval gives you more options when it comes to selecting the individual patches, but automation is a great choice if you're looking for convenience.
If you're approving patches manually, it’s good practice to start approving them from the most recent ones and pay attention to possibly superseded patches. This way you can easily avoid the deployment of unnecessary patches that have already been replaced by newer ones.
If your patch approval process is automatic, available patches are deployed to pilot devices automatically based on your configurations.
6. Patch testing and pilot group
To ensure that all patches work as they should, run a pilot for a selected number of devices before installing new patches on everyone's devices. Make sure that you have a diverse set of test or pilot devices. This helps you ensure the patches’ compatibility with all business-critical applications on all affected operating systems. If possible, also include some business-critical systems in your pilot group but make sure that they are easily recoverable if any problems occur.
Pay attention to the users of the pilot computers when choosing the pilot systems. Try to select pilot devices whose users are tech-savvy and perceptive. Remember to inform the users about the upcoming deployments so that they are aware of what’s going on and ready to report any possible problems without delay.
If any problems occur, do not approve the patch for other computers before investigating the issue more closely.
7. Patch distribution
If no issues occur during the pilot, you can deploy the patches to all of your devices. We recommend deploying them first to a selected group of devices to make sure that everything is working as it should. With patch management software, you can automate the deployment process to different device groups.
Remember to always have a patch rollback plan prepared in case of unexpected issues.
8. Patch compliance status
After the deployment, make sure that all of the patches have been installed successfully. With patch management software, you can easily get a report of the status of your devices.
Automated patch management with Miradore
Miradore offers automated patch management for Windows and Mac — helping you to keep your Windows computers secure and running smoothly. Patch management is available for Microsoft products, such as the Windows operating system, and over 200 other software products from almost 100 vendors, like Adobe, Cisco, Citrix, Google, and Oracle as well as MacOS.
With Miradore, you can centrally manage patches for your Windows and Mac devices in four steps: Detect, Report, Pilot, and Deploy.
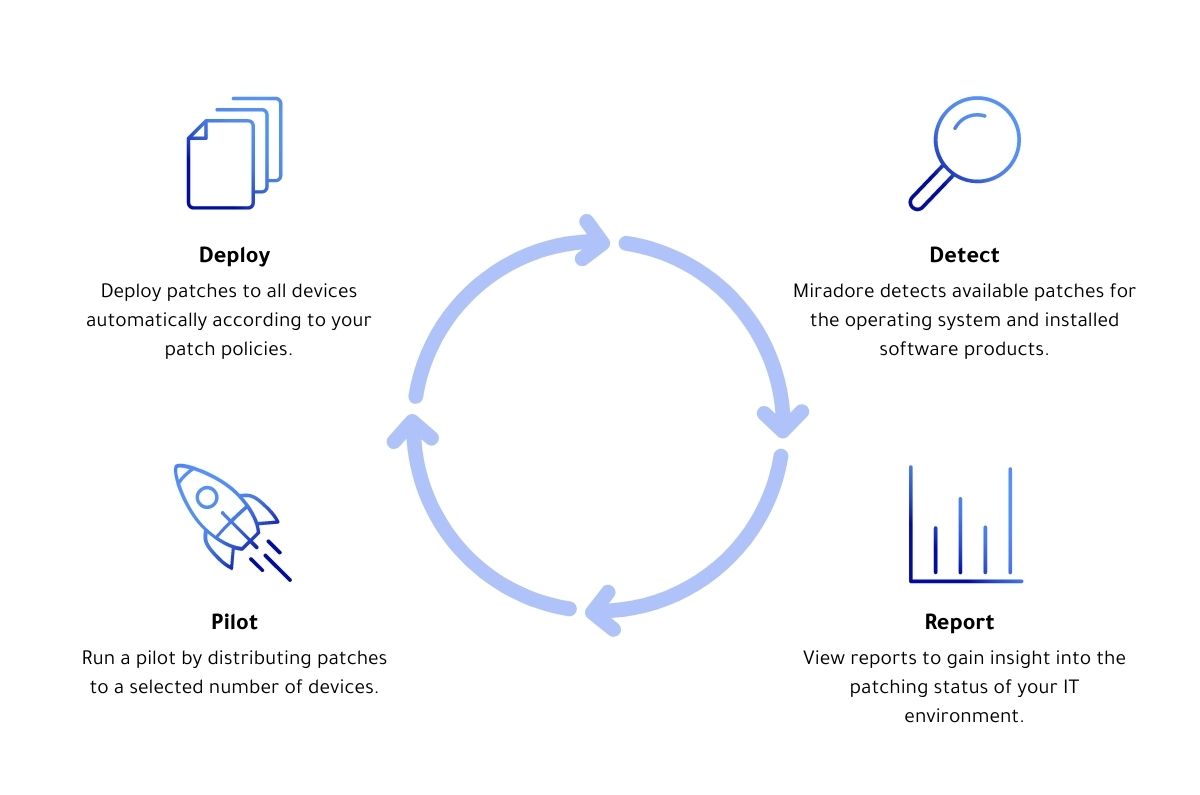 Miradore patch management process
Miradore patch management process
1. Detect
Miradore retrieves a list of software updates and patches from supported vendors automatically. Patches are retrieved in a pre-packaged format ready for automatic deployment, clearly presented in one consolidated view. Using the list of available patches, Miradore scans the patching status of your Windows and Mac devices daily, without causing disruption to device users.
2. Report
Miradore monitors all managed devices, giving administrators a clear view of the patching status. Miradore provides easy-to-understand reports and widgets displaying information on the availability and installation status of patches.
3. Pilot
You can use Miradore’s pilot testing feature to distribute the patches first to a group of pilot devices before upgrading all devices. This way you can minimize possible problems caused by patches. If you find out that some patches cause problems, you can block them by using patch blacklisting.
4. Deploy
You can configure Miradore to deploy applicable patches to your Windows and Mac devices automatically. You only need to define very basic rules for patching, such as the delay for the installation and which groups of devices should be patched. The system takes care of the actual installation part automatically, with minimal disruption to the device user. At the time of installation, devices will download the patch installation media directly from the vendor.
Miradore's patch management feature supports Windows 7, Windows 8, Windows 10, and Mac. Patch detection and reporting are included in the Free plan but you can test out the full patch management feature risk-free with our 14-day Premium trial.
