You can use Miradore configuration profiles to manage and distribute restrictions and settings to your managed devices. In addition to built-in configuration profiles for Windows, you can customize or extend the management capabilities by creating custom policies in Miradore. For example, you can define what is allowed or denied in your managed Windows devices or how they behave, look and feel.
Important information
Windows Configuration Service Provider (CSP) enables IT admins to configure multiple custom policies for Windows 10 and 11 devices. These CSP-based policies use Open Mobile Alliance - Uniform Resource Identifiers (OMA-URIs), which are paths to the specific settings in Windows. With Miradore, you can build the OMA-URI in a configuration profile and add a new custom policy easily for your managed Windows device.
Miradore supports Policy CSPs, excluding policies starting with ADMX_. It is also important to note that there is variation in the supported policies between different Windows versions. The features of the Windows 10 and 11 editions differ from each other, and new policies come along with new version releases. You can find the information and requirements of each policy from Microsoft policy CSP documentation.
If both an MDM-based CSP policy and its equivalent Group Policy (GP) are set on a device, the group policy wins over the CSP policy by default. However, IT administrators can use the ControlPolicyConflicts policy to ensure that the MDM-based CSP policy wins over the GP if there is a conflict.
Requirements
- Miradore Premium plan
- Windows 10 or 11
- Full management
How to create a custom policy configuration?
Start creating a new configuration from the Configuration profiles page on Miradore. Click Add, choose the platform, and then Custom policy.
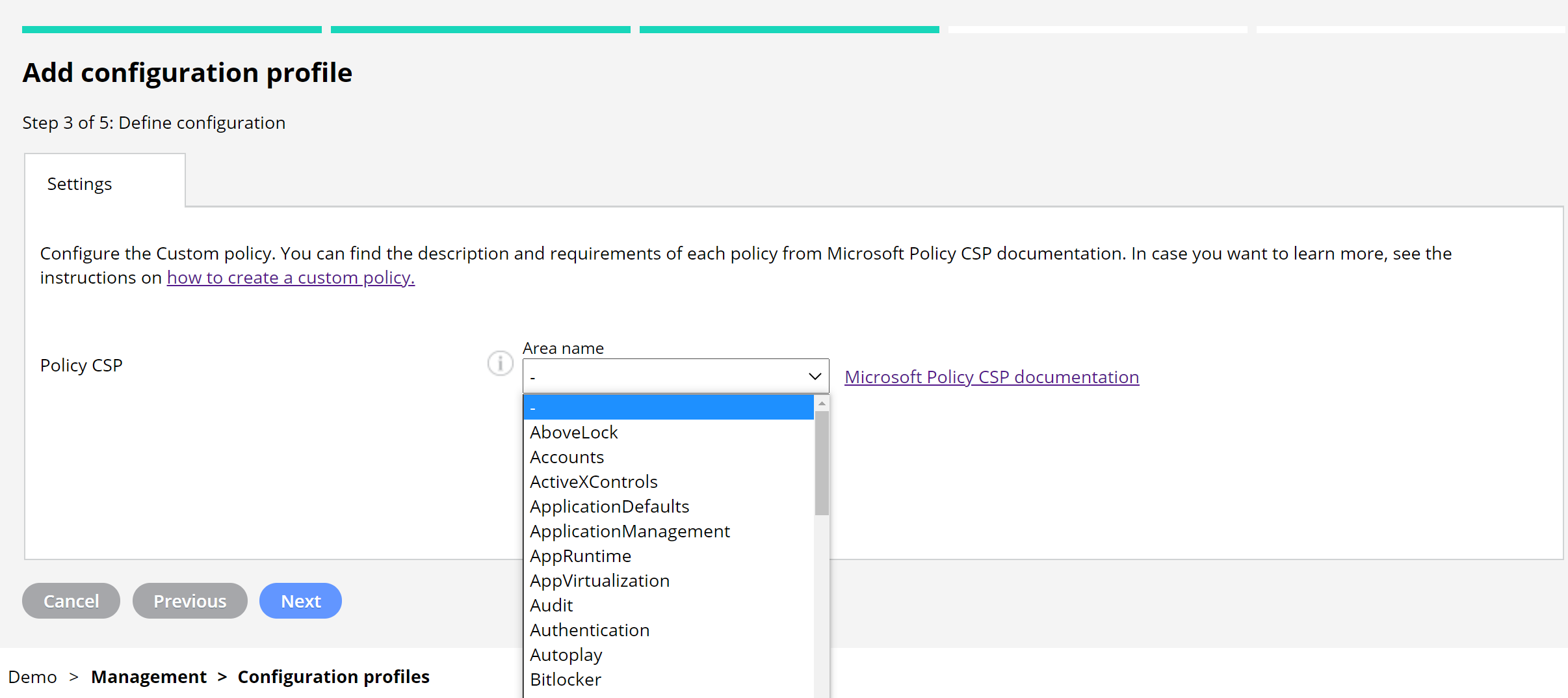
1. Define the type of configuration in the Policy CSP (build the OMA-URI).
-
-
- Choose the Area name from the drop-down menu. All available policies to configure with Miradore are included in the dropdown menu.
- Check the policies and requirements from Microsoft's documentation. When you have chosen the Area name, the link takes you to the selected area in the documentation to find and copy the correct Policy name.
-
![]()
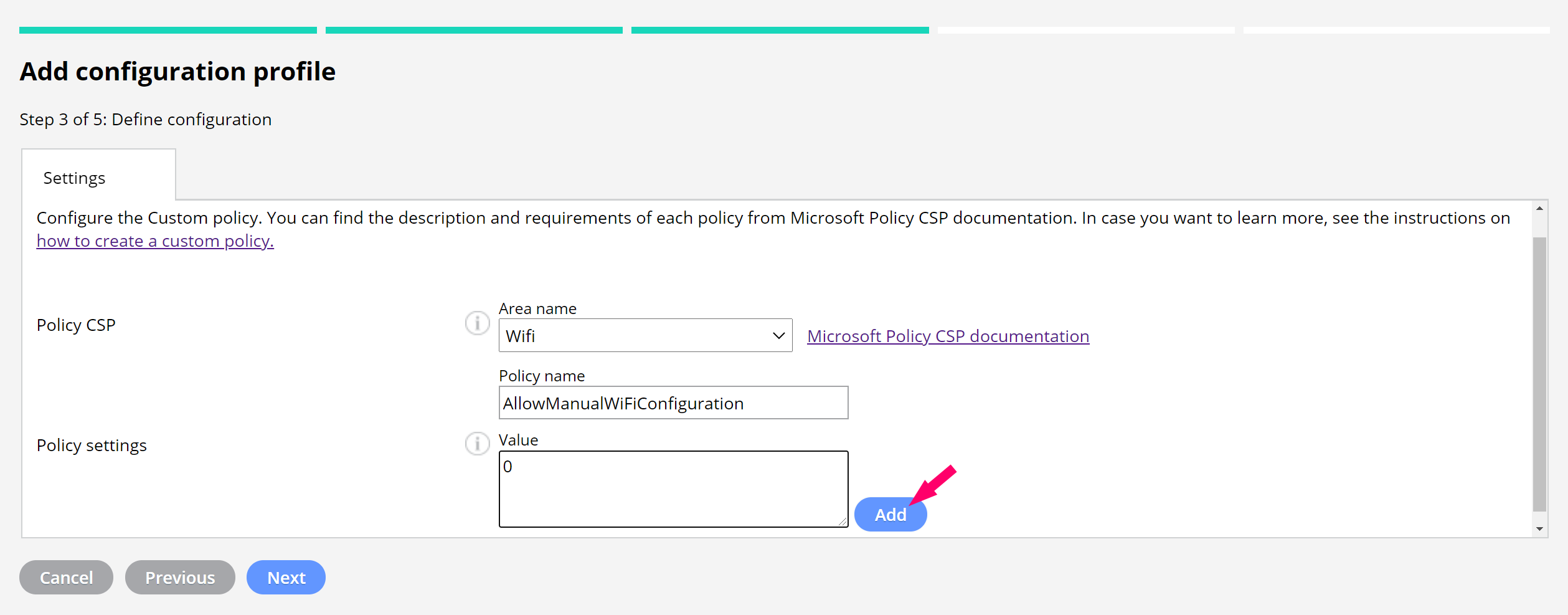
2. Define the Policy settings by entering the value and press Add. You can add multiple name/value pairs of the policy area in one custom policy.
The Microsoft Policy CSP documentation provides information about the supported values.
How to create a custom ADMX-backed policy configuration?
Some ADMX-backed policies are supported, but you need to construct the required payload manually. Our example is related to the system hibernation timeout and battery settings.
-
-
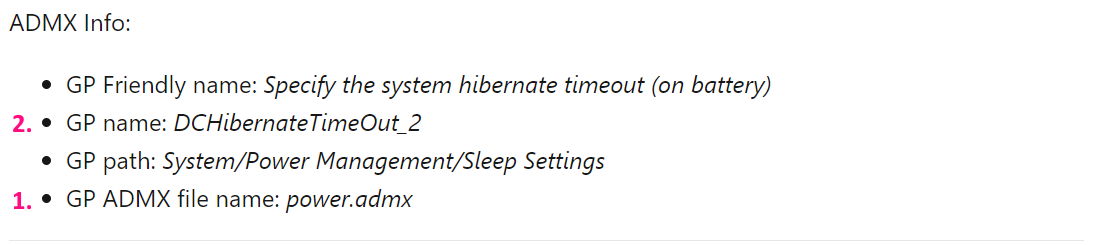
- Find out the info from the Microsoft Policy CSP document.
-
Example: Create a policy that defines the inactivity period before Windows transitions to hibernate in the device on a battery.
-
-
- Each Windows device has a folder including a bunch of ADMX files (C:\\Windows\PolicyDefinitions). GP ADMX file name tells you the correct file for searching the input for the value field.
- The GP name shows the policy name you need to look for from the file, in this case, DCHibernateTimeOut_2. Inside the <elements> tag, you can find the configurable values. There can be several values, but for this example, there is only one:
-
<elements>
<decimal id="EnterDCHibernateTimeOut" valueName="DCSettingIndex" required="true" maxValue="4294967295" />
</elements>
The value to enter to the custom configuration:
<enabled /><data id=“EnterDCHibernateTimeOut” value=“TimeInSeconds”></data>
You can find more information about ADMX-backed policies and how to create the required XML value from Microsoft's documentation.
When you have created the policy, you may deploy it to managed devices as any other configuration profile in Miradore.
Read the article on how to prevent unenrollment of the MDM profile on Windows 10 and 11, in case you like to see more examples about the configuration.
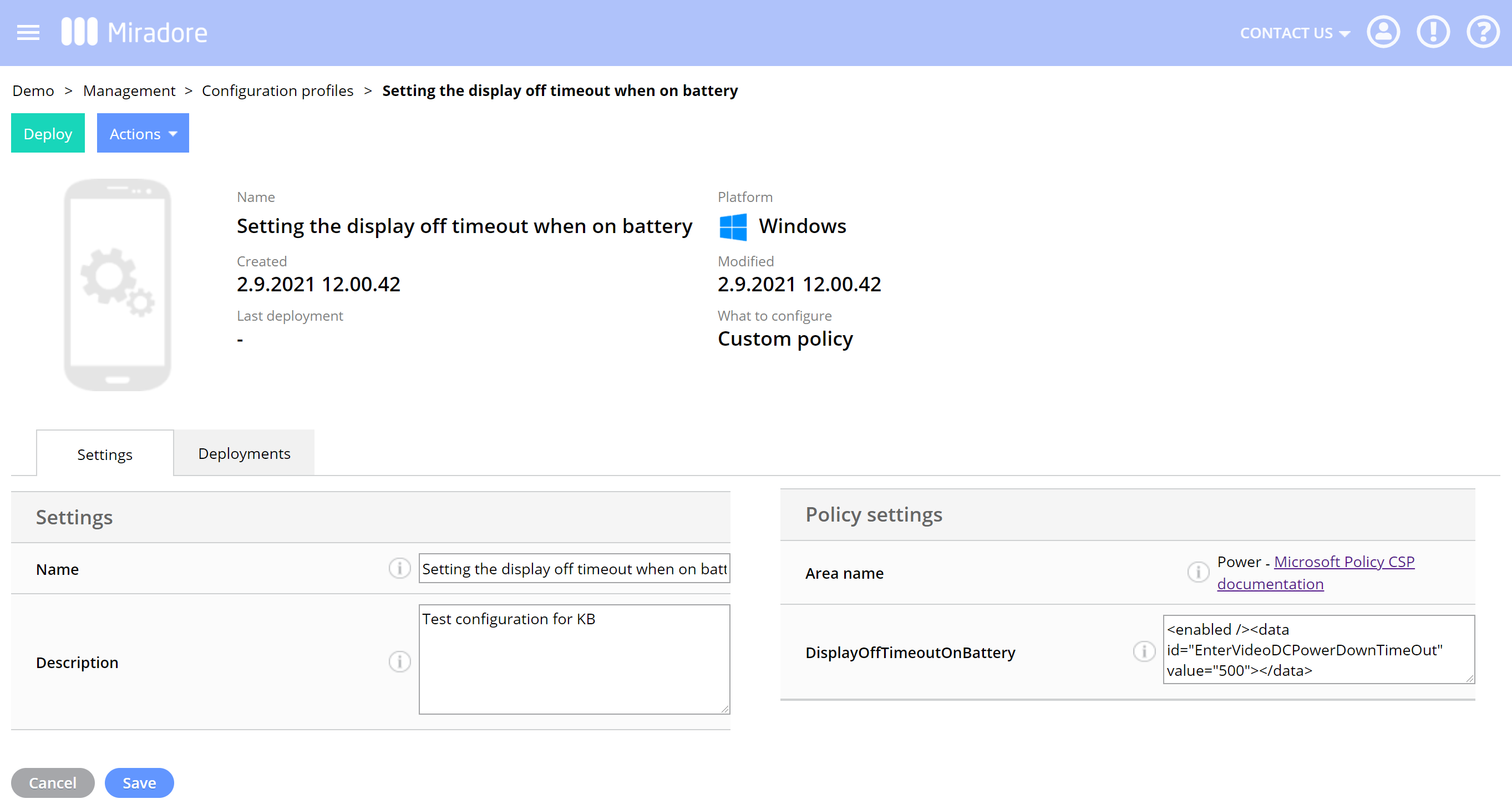
Updating the policy configuration
You can edit the values of the existing policies, but you can not add or remove policies from the policy configuration. Go to Management > Configuration profiles > Configuration profile to edit the configuration.
Custom CSP example
To see an example of a custom CSP, please see the How to make MDM profile non-removable on Windows 10 and 11 article. In the example, we explain how you can make the work account non-removable and prevent users from disabling the management.
Another supported type would be Storage/RemovableDiskDenyWriteAcces as seen below:
Area Name: Storage
Policy name: RemovableDiskDenyWriteAccess
Value: 1
For further information please see Microsoft policy csp / power / hibernation documentation.
Different policy types
To read more about the configuration service provider (CSP) policies available on Windows 10 and Windows 11 please see Microsoft client management documentation.
-
We don't currently support any other than Policy CSP
-
We don't support policies starting with "ADMX_"
-
There are ADMX backed -policies, that is different from policies starting with ADMX_. For further information please see the Understanding ADMX policies article by Microsoft.
-
There are policies that are really simple to use as the values are just simple numbers or such
Removing custom configuration policies
When you remove custom configuration policies be extra careful.
Have feedback on this article? Please share it with us!
Previous Article:
« Windows 10 password policy for local accounts
Next Article:
Policy CSP example: How to make MDM profile non-removable on Windows 10 and 11 »