This article explains how you can block the use of personal Google accounts on managed devices, or allow the use of personal Google accounts, but just block their access to the public Google Play store.
When this is needed?
The typical scenario is that your organization has defined an enterprise app store to manage Android devices using managed Google Play. The managed Google Play store is basically a more controlled version of the public (consumer) Google Play store, letting your IT admins decide which apps are available for device users in the store.
Although the managed Google Play store is present, device users can, by default, also access the public Google Play store using a personal Google account - which may be considered to negate the benefits of having the enterprise app store.
In order to address this loophole, you can deny the use of personal Google accounts on Android devices entirely, or allow their use but just block access to the consumer version of the Play Store. The latter option is viable if you, for example, want to allow the users to configure their personal Gmail accounts to the device.
Requirements
- Premium subscription of Miradore
- Applicable to Android devices which have either Android Enterprise Work Managed Device (Full enrollment) or Work Profile mode (Light enrollment) of management enabled through Miradore
- Miradore Client version 2.7.9 or later
Steps to restrict the use of personal Google accounts
- In Miradore, navigate to Management > Configuration profiles and use the blue Add button to create a new configuration profile. Select Android platform.
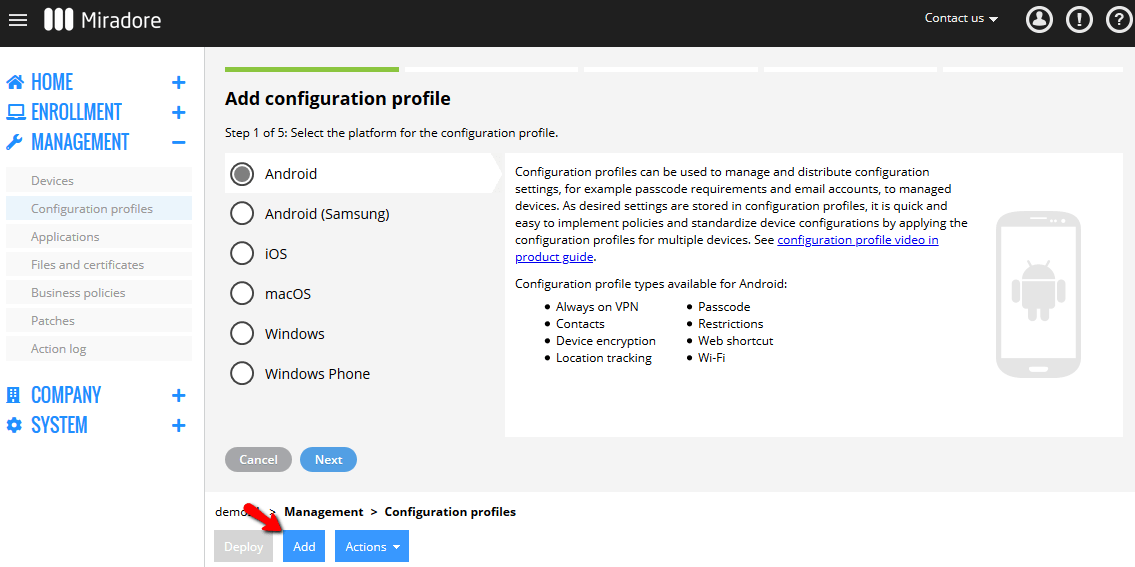
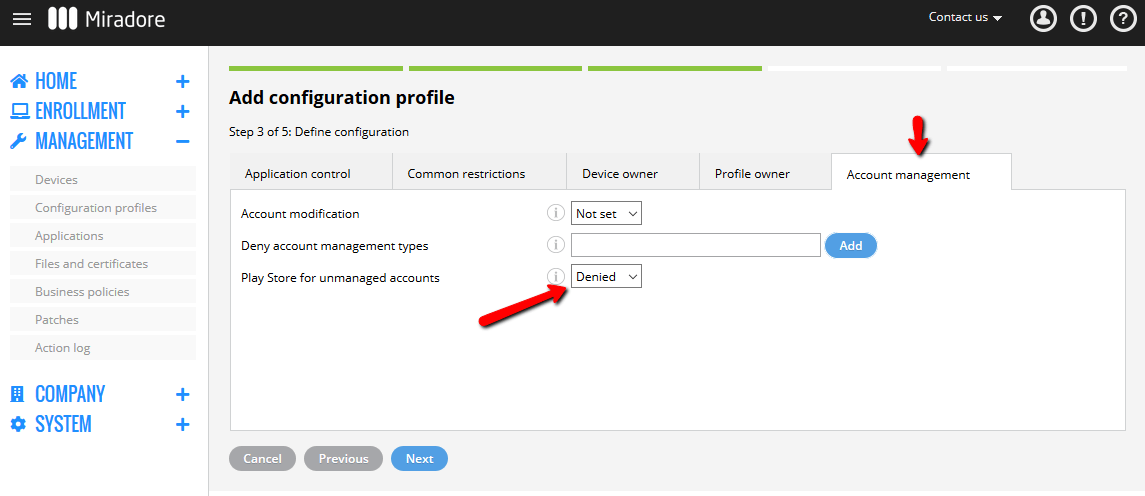
- Choose Restrictions and go to the Account Management tab. There you can configure what the device user(s) are allowed or forbidden to do on the device. Account modification: Set this to "Denied" if you want to prevent the device user(s) from making any changes to the accounts configured for the device. This is the strictest restriction. Deny account management types: With this setting, you can prevent the device user(s) from managing certain types of accounts on the device. For example. "com.google" would block device user(s) from adding a personal Google account to the device.Other examples:
- com.google.android.gm.pop3 (deny adding/modifying POP3 accounts)
- com.google.android.gm.legacyimap (deny adding/modifying IMAP accounts)
- com.google.android.gm.exchange (deny adding/modifying Exchange accounts)
- com.facebook.auth.login (deny adding/modifying Facebook accounts)
- com.google.work (Deny adding/modifying managed Android Enterprise accounts)
- com.samsung.android.email (deny adding/modifying Samsung email accounts)
- com.osp.app.signin (deny adding/modifying deny adding/modifying Samsung accounts)
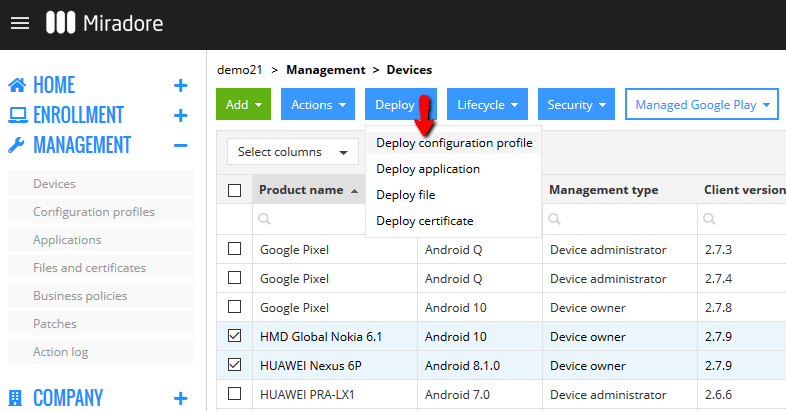
- com.samsung.android.exchange (deny adding/modifying Samsung Exchange accounts)Play store for unmanaged accounts: Set this to "Denied" if you want to prevent device users from accessing the consumer version of the Google Play store using their personal Google Accounts. In this case, they can only access the managed Google Play store. This restriction allows the device users to add their personal Google account to the device if they want to use other Google services with the personal account. Example configuration in the picture below. - Click Next and give a name and description for the profile. After that, you can distribute the restriction to desired devices using the Deploy > Deploy configuration profile option from the page toolbar.

Worth noting that you can check the device management mode and client version from the Client version and Management type columns of the Devices page.
Device owner = Work Managed Device
Profile owner = Work profile
Have feedback on this article? Please share it with us!
Previous Article:
« Preventing the removal of managed Google Play account
Next Article:
Kiosk Mode for Android (Samsung) »