Solutions
What is CJIS? And how to become CJIS compliant?
Government entities, especially law enforcement or criminal justice agencies must often adhere to even stricter security standards than large corporations. It is no surprise then that ensuring devices with access to, or that operate in support of, criminal justice services and information adhere to the CJIS compliance policy.
What is CJIS?
Established by the FBI in 1992 out of the former Identification Division, the Criminal Justice Information Services Division also known as CJIS, consists of state-of-the-art tools and services designed to support law enforcement, the intelligence community, and the general public. The CJIS division acts as the central repository for criminal justice information and contains other programs such as the National Crime Information Center (NCIC), the National Instant Criminal Backgroud Check System (NICS), and the Law Enforcement Enterprise Portal (LEEP) to name a few.
However, in order for organizations to use or access these services they must be or become CJIS compliant. CJIS compliance is achieved by adhering to the Criminal Justice Information Services (CJIS) Security Policy.
Why is CJIS compliance important?
Data and device security are extremely important in the business world and even more so in matters regarding government and law enforcement. Mobile devices are susceptible to a number of threats, threats like:
- Loss, theft, or disposal
- Unauthorized access
- Malware
- Spam
- Electronic eavesdropping / tracking
These weaknesses in device and data security must be accounted for in order to prevent the improper use of Criminal Justice Information (CJI), which could comprise the health and safety of law enforcement and the general public. This is why it is crucial for any and all organizations that access, transmit, store, or create criminal justice information to adhere to the controls laid out in the CJIS Security Policy.
Should an entity be found to be non-compliant they can be denied use of CJI services and data. This would prohibit them from accessing the information on wanted persons, stolen vehicles, driver’s license data, missing persons, and much more.
Is your MDM CJIS compliant?
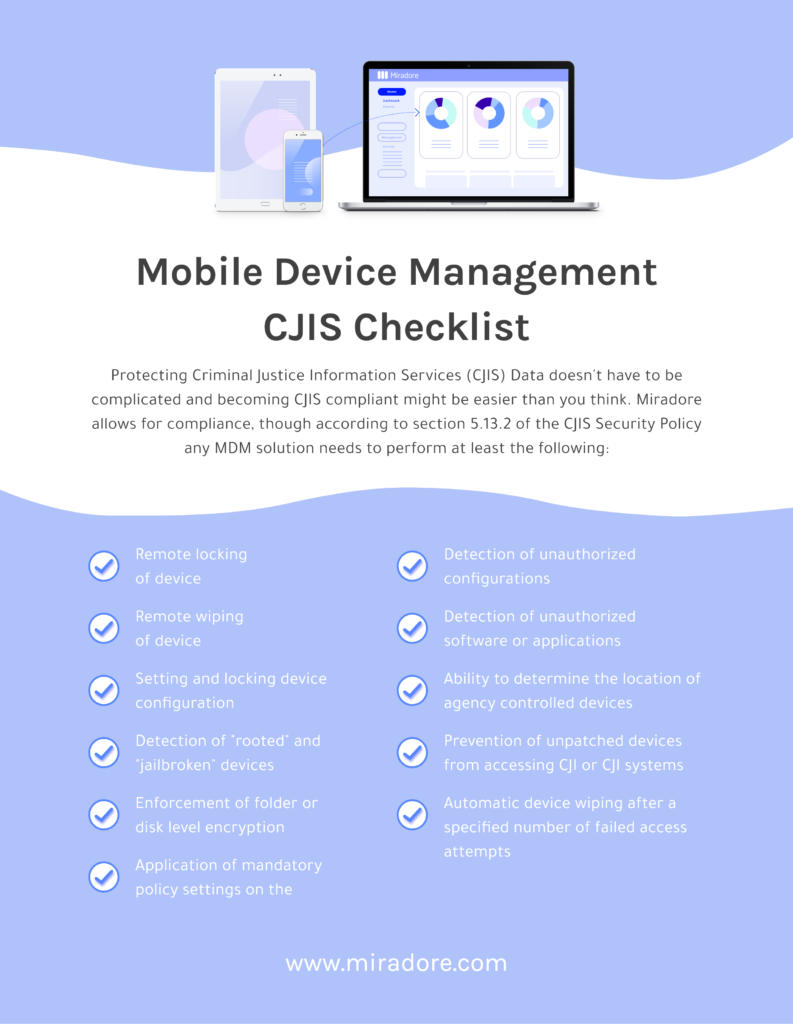
The CJIS Security Policy provides controls to protect the full lifecycle of criminal justice information and as such it requires that MDMs strictly adhere to them. Section 5.13.2 Mobile Device Management (MDM) of the Criminal Justice Information Services Security Policy details the features and functions an MDM must be able to perform for it to be deemed CJIS compliant. Download our CJIS checklist to see if you or your current MDM meet the minimum requirements (last updated 03.12.2021).
Miradore currently works with companies seeking CJIS compliance. If you have any questions regarding CJIS and mobile device management, our team would be happy to discuss the subject with you in more detail. Please fill out the form below and we will get back to you as soon as possible.